QIDSecure - Agentic Security
QIDSecure — Quantum Identity
for AI Agents
The machines have outnumbered the humans. The identity infrastructure securing them hasn't caught up. QIDSecure closes that gap — with quantum physics.
An identity crisis at unprecedented scale
Enterprises are deploying AI agents that log into systems, fetch data, execute transactions, modify code, and delegate tasks to other agents — all at machine speed, with minimal human oversight. These are not experimental toys. They are production infrastructure handling real data, real money, and real decisions.
Every one of these agents authenticates with a credential — an OAuth token, a session key, an API .key, a certificate. And every one of those credentials begins with a random number. Today, that random number comes from a PRNG: a deterministic algorithm with exploitable patterns.
The scale of the exposure is staggering. Non-human identities outnumber human users by 100:1 to 500:1. A single enterprise generates millions of credential events daily. If the randomness behind those credentials is algorithmic, every credential in the system shares the same foundational weakness — and a single PRNG compromise cascades across the entire agent fleet.
This is not a theoretical risk. Nearly half of enterprise teams still use shared API keys for agent authentication. Most agent frameworks rely on default OS-level PRNGs for token generation. And AI-accelerated attacks are making it faster and cheaper to find patterns in algorithmic randomness. The identity systems built for human users were never designed for this scale, this speed, or this threat model.
identity ratio
enterprises
API keys for agents
A compromised human credential exposes one user's access. A compromised agent credential exposes machine-speed exfiltration across every system that agent touches — databases, cloud accounts, APIs, payment systems — in seconds, not hours.
NIST's post-quantum cryptography standards demand significantly larger entropy blocks than classical algorithms. PRNGs cannot reliably provide this at machine scale. Weak entropy undermines PQC strength regardless of the algorithm used.
QIDSecure: quantum entropy at the foundation
of every agent credential
QIDSecure replaces the algorithmic randomness at the root of every agent credential with hardware-rooted quantum entropy from QCoreSecure's silicon-photonics QRNG chip. The random numbers seeding your agent's keys, tokens, and certificates become physically impossible to predict or reproduce — making the credentials themselves unbreakable.
But QIDSecure goes further than just better randomness. It wraps the entire agent credential lifecycle in a zero-trust verification architecture that assumes the endpoint is already compromised. Every agent action is signed with an ephemeral key that exists for milliseconds, then checked by a server-side gateway that validates session, scope, and entropy provenance before any action executes.
No agent credential can be forged or predicted without real-time access to the QCoreSecure quantum entropy source.
How QIDSecure Works
Quantum Handshake
Agent establishes a PQC-encrypted session with the quantum entropy source via ML-KEM key exchange. Immune to harvest-now-decrypt-later interception.
Ephemeral Key Derivation
For every task, fresh 256-bit quantum entropy generates a new ML-DSA signing key pair. The key is used exactly once, exists in memory for milliseconds, then is securely destroyed. No long-lived secrets on the endpoint.
Action Signing
Every agent command is hashed together with its authorised scope and a timestamp, then signed with the ephemeral key. This creates a tamper-evident action manifest that proves what the agent intended to do.
Gateway Verification
A server-side trust anchor independently validates three things: is the session valid, did the entropy come from a real quantum source, and is this action within the agent's authorised scope. Any failure blocks the action instantly.
Audit & Revocation
Every signed action is logged in a tamper-evident trail. If an agent is compromised, a single click revokes its quantum entropy session — the agent cannot generate new credentials and is neutralised across all systems simultaneously.
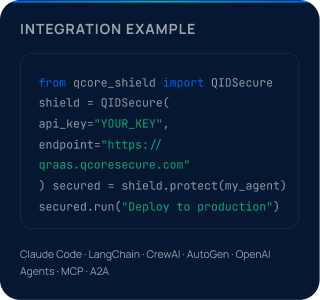
Three Lines of Code
QIDSecure wraps any agent framework. No infrastructure changes. No key management overhead. The SDK handles the quantum handshake, key derivation, and action signing automatically.
Deployment Tiers
RESTful quantum entropy. Integrates with Auth0, Vault, CyberArk.
On-prem entropy cache with cloud sync. Recommended for agent fleets.
Local QRNG chip. Zero network.
- No credential can be forged without access to the quantum entropy source
- One-click kill switch neutralises any compromised agent across all systems
- Full audit trail satisfying EU AI Act, SOX, PCI DSS, OWASP Agentic AI
- Drop-in integration — three lines of code, any agent framework
Enterprise Governance Console
The CISO's command centre for agent identity. Complete visibility and control over every agent in your fleet.
Entropy Heartbeat
Real-time status of all QRNG sources — cloud endpoints, hybrid gateways, on-premise appliances. Throughput, health, NIST compliance validation. SOC-display ready.
Agent Identity Registry
Live inventory of every QIDSecure agent: identity, location, active session, authorised scope, last action, PQC status. Full lifecycle governance enforced.
The Kill Switch
One click revokes an agent's quantum entropy session. No new credentials can be generated. Agent neutralised across all systems simultaneously. Zero-propagation revocation.
Audit trail: EU AI Act · SOX · PCI DSS · OWASP Agentic AI · FIPS 140-3
Integration Model
QIDSecure doesn't replace your identity stack. It hardens the cryptographic foundation beneath it — plugging into the platforms you already use.
Identity Providers
OIDC, SAML, OAuth 2.1 — quantum entropy for token minting, PKCE verifiers, session IDs. Replaces PRNG backend in Auth0, Okta, CyberArk.
Secret Managers
PKCS#11, KMIP, REST — API key generation, secret rotation, encryption keys. Integrates with HashiCorp Vault, 1Password.
Agent Orchestration
MCP, A2A Protocol, REST — credential issuance, ephemeral identity tokens, delegation chain security across multi-agent architectures.
HSMs / KMS
PQC key generation, certificate signing, master key seeding via PKCS#11 and proprietary HSM APIs.
PKI / CAs
EST, ACME, SCEP — ephemeral agent certificates, SPIFFE/SPIRE identity documents. Quantum-hardened signing operations.
Network Security
QRNG Open API (Palo Alto Networks) — session key seeding, IKE handshake entropy, TLS ticket keys.
Ready for Quantum-Grade Security?
Whether you’re securing encryption keys, AI agent credentials, or critical infrastructure — start with randomness rooted in physics.
To connect with us, simply complete the form.
